New Cyber Attacks Target Ivanti Connect Secure VPN Vulnerabilities
Cybersecurity Threats and Vulnerabilities
Ivanti Connect Secure VPN Exploitations
In January 2025, Ivanti disclosed critical vulnerabilities in the Ivanti Connect Secure VPN, specifically CVE-2025-0282 and CVE-2025-0283. These vulnerabilities, which include an unauthenticated stack-based buffer overflow, have been actively exploited in the wild since mid-December 2024. The successful exploitation of these vulnerabilities permits remote code execution, potentially leading to the compromise of an entire network.
Mandiant has identified UNC5221 as a suspected China-nexus espionage actor linked to these incidents. They previously exploited vulnerabilities such as CVE-2023-46805 and CVE-2024-21887 to gain unauthorized access.
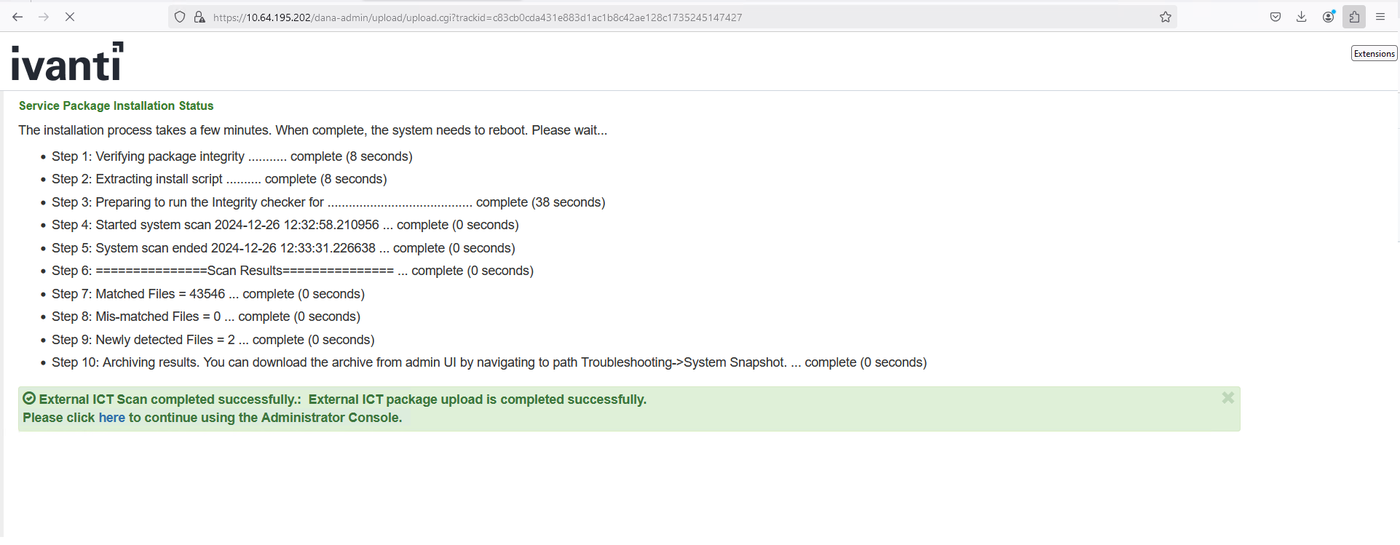
Immediate actions recommended by Ivanti include the use of their Integrity Checker Tool (ICT) and contacting support if suspicious activity is detected.
Threat Actors Exploiting Multiple Vulnerabilities
The Cybersecurity and Infrastructure Security Agency (CISA) and the FBI released a joint advisory in response to exploitation of vulnerabilities in Ivanti Cloud Service Appliances (CSA). The vulnerabilities include CVE-2024-8963, an administrative bypass, and CVE-2024-9379, a SQL injection vulnerability. Threat actors have exploited these vulnerabilities to gain access, execute remote code, and implant web shells.
Ivanti CSA versions 4.6x prior to 519 are affected, and organizations are urged to upgrade to the latest supported versions. Threat actors have utilized chains of vulnerabilities, exploiting these weaknesses to conduct malicious activities, including lateral movement within networks.
Cyber Attack Trends
Recent reports indicate a rise in sophisticated cyber attacks. Notable trends include:
- Investment Scams: A wave of online investment scams is leveraging fake news outlets to trick users.
- Malware Attacks: The use of APK malware for remote command execution has been observed through extensive domain exploitation.
- WordPress Exploits: Hackers are exploiting vulnerabilities in WordPress sites to redirect users to malicious websites.
Organizations are advised to remain vigilant and utilize security products that can break these attack sequences and facilitate threat hunting.
Notable Cybersecurity Alerts
C-DATA Web Management System RCE Attack: This attack targets a vulnerability in the C-DATA system, allowing remote code execution. Read more here.
Akira Ransomware: This ransomware targets small to medium-sized businesses, employing tactics like Ransomware-as-a-Service. Details can be found here.
PAN-OS GlobalProtect Command Injection Vulnerability: This critical vulnerability allows unauthenticated OS command injection on PAN-OS devices. Learn more.
ConnectWise ScreenConnect Attack: Critical flaws in remote management software ScreenConnect have been exploited for malicious purposes. Read the full report.
Organizations should adopt proactive measures to assess their cybersecurity postures and invest in robust security solutions to combat these increasing threats. For tailored solutions, consider exploring the offerings of undefined.





