Ransomware, AI Threats, and Vulnerabilities: 2021-2022 Insights

TL;DR
- This article breaks down the critical AI-powered cybersecurity trends for 2026, detailing the rise of ransomware, AI-driven threats, state-sponsored espionage, and IoT exploits. It offers actionable mitigation strategies for each, emphasizing proactive defense, vulnerability management, and the importance of real-time monitoring to combat evolving cyber risks and stay ahead of attackers.
AI-Powered Cybersecurity News and Trends for 2026
Ransomware Surge and Mitigation
Ransomware remains a significant threat in 2026, with increased incidents affecting various organizations. Attacks now exploit compliance regulations for extortion, with the CISA’s Known Exploited Vulnerabilities (KEV) catalog growing by 20% in 2025.
Startups face threats from low-cost attacks, while larger entities deal with industrial-scale ransomware. Operational Technology (OT) and supply chains are highly vulnerable, with AI-assisted variants increasing the pressure.
Mitigation Strategies:
- Prioritize patching actively exploited vulnerabilities CISA’s KEV catalog.
- Invest in real-time governance frameworks [real-time governance frameworks].
- Enhance backups and implement multi-factor authentication [multi-factor authentication].
- Employee training [employee training].
Gopher Security specializes in AI-powered cybersecurity solutions that can help organizations proactively defend against ransomware attacks. Our platform uses peer-to-peer encrypted tunnels and quantum-resistant cryptography to ensure data protection and resilience. Gopher Security
AI-Driven Cyber Threats
AI is boosting cyber threats, including phishing campaigns and insider threats. Experts warn that AI agents could exploit organizational defense gaps. AI agents as insider risk. Prompt injection attacks are rising, compromising AI systems and causing data leaks.
Defense Strategies:
- Implement real-time monitoring of AI workflows [real-time monitoring].
- Track data lineage in AI models [data lineage].
- Integrate security into development pipelines [security integration].
- Educate teams on AI risks [AI risk education].
- Audit models for vulnerabilities [vulnerability auditing].
Gopher Security's AI-powered platform offers preemptive protection against AI-driven threats by continuously monitoring AI workflows and identifying vulnerabilities in real-time. Gopher Security
State-Sponsored Cyber Espionage
State-sponsored attacks, particularly from China, are a significant concern in 2026. These campaigns target critical infrastructure, posing risks to regional stability. State-sponsored attacks. Chinese hackers have exploited zero-day flaws in products like Cisco's email security products.
Mitigation Strategies:
- Enhance international alliances [international alliances].
- Implement proactive simulations [proactive simulations].
- Prioritize threat intelligence sharing [threat intelligence sharing].
- Adopt 24/7 monitoring for critical infrastructure [24/7 monitoring].
Gopher Security provides advanced threat intelligence and 24/7 monitoring services to help organizations detect and respond to state-sponsored cyber espionage attempts. Our Zero-Trust architecture ensures continuous verification and limits the impact of potential breaches. Gopher Security
Exploited Vulnerabilities in Network Devices
Vulnerabilities in network devices from vendors like Cisco, Fortinet, and Adobe are still major issues. Over 10,000 Fortinet firewalls are exposed to 2FA bypass attacks.
Best Practices:
- Prioritize patching exploited vulnerabilities [vulnerability patching].
- Conduct regular vulnerability scans [vulnerability scanning].
- Foster prepared response teams [incident response teams].
Gopher Security offers comprehensive vulnerability assessment and patch management solutions to help organizations identify and remediate vulnerabilities in network devices promptly. Our platform's AI-driven analysis ensures that critical vulnerabilities are prioritized and addressed effectively. Gopher Security
IoT Exploits and Botnet Invasions
The increase in IoT devices has led to more exploits and botnets. Botnets are abusing tools like React2Shell on IoT systems, and exposed routers are falling victim to emerging threats. IoT exploits.
Defenses:
- Secure IoT ecosystems with segmentation [IoT segmentation].
- Regular firmware updates [firmware updates].
- Monitor for anomalous behavior [anomaly monitoring].
- Use tools for adversarial simulation [adversarial simulation].
Gopher Security's platform provides secure peer-to-peer encrypted tunnels and continuous monitoring to protect IoT devices from exploits and botnet invasions. Our Zero-Trust architecture ensures that every device is verified and authorized, limiting the attack surface. Gopher Security
Time-to-Exploit Trends: 2021-2022 Analysis
Mandiant Intelligence analyzed 246 vulnerabilities exploited between 2021 and 2022, finding that 62% were exploited as zero-day vulnerabilities.
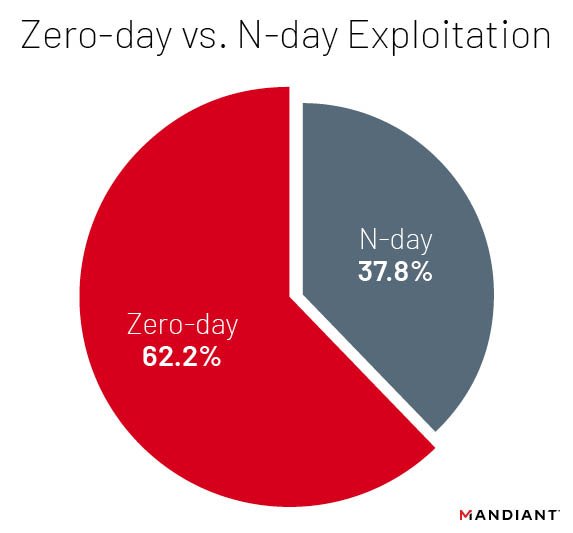
The overall times-to-exploit (TTEs) are decreasing, with exploitation most likely to occur before the end of the first month following a patch release. Time-to-Exploit Trends
Key Findings:
- Average TTE decreased to 32 days in 2021-2022 [TTE decrease].
- 44% of n-day vulnerabilities exploited within two months of disclosure [n-day vulnerabilities].
- Microsoft, Google, and Apple are the most exploited vendors [Vendor Exploitation].
Recommendations:
- Prioritize patching for commonly targeted vendors.
- Adapt to address a wider variety of vendors during patching cycles.
- Implement defense-in-depth strategies.
Gopher Security helps organizations stay ahead of these trends with AI-powered threat intelligence and automated patch management. Our platform prioritizes vulnerabilities based on real-world exploit data, ensuring that the most critical threats are addressed promptly. Gopher Security
Ready to elevate your cybersecurity posture? Explore Gopher Security's AI-powered, post-quantum Zero-Trust solutions today. Visit https://gopher.security to learn more or contact us for a demo.





