FBI Seizes RAMP Ransomware Forum Linked to Cybercrime Operations

TL;DR
- The FBI, in collaboration with the US Attorney's Office and the DoJ, has seized RAMP, a significant dark web forum used by numerous ransomware groups. This takedown disrupts criminal infrastructure, particularly affecting lower-tier actors, though top-tier groups may migrate to other platforms like Telegram. The operation provides valuable intelligence for law enforcement, highlighting ongoing efforts against cybercrime.
FBI Shuts Down RAMP Ransomware Forum
The FBI has seized the Russian Anonymous Marketplace (RAMP), a notorious cybercrime forum known for allowing ransomware-related discussions. The seizure was a collaborative effort involving the US Attorney’s Office for the Southern District of Florida and the US Justice Department’s (DoJ) Computer Crime and Intellectual Property Section (CCIPS).

The seizure is highlighted by a banner stating "This site has been seized," accompanied by a taunt directed at RAMP operators: "The Only Place Ransomware Allowed!" and an image of Masha from the Russian cartoon "Masha and the Bear." Domain names linked to RAMP now redirect to seizure notices with FBI and DoJ seals, and the nameservers have been updated to ns1.fbi.seized.gov and ns2.fbi.seized.gov.
RAMP's Role in the Cybercrime Landscape
RAMP gained prominence in 2021 after other major dark web forums like XSS and Exploit, as well as BreachForums, banned ransomware discussions. RAMP became a hub for new and low-to-mid-tier ransomware groups to promote themselves and offer services.
According to Yelisey Bohuslavskiy, co-founder of Red Sense, RAMP was created by individuals affiliated with Russian security services as a response to the ransomware-as-a-service (RaaS) sprawl. Tammy Harper, a senior threat intelligence researcher at Flare, described RAMP as “one of the most trusted ransomware-adjacent forums in the cybercrime ecosystem.” The forum supported the entire attack chain, offering a marketplace for stolen credentials, malware promotion, and ransomware services, as noted by Ben Clarke, a security operations center (SOC) manager at CybaVerse.
Several notorious ransomware groups, including LockBit, ALPHV/BlackCat, Conti, DragonForce, Qilin, Nova, Radiant, and RansomHub, reportedly operated on the forum.
Key Individuals Behind RAMP
One of the individuals behind RAMP was Mikhail Matveev, a Russian national known as Orange, Wazawaka, and BorisElcin. Matveev was arrested in Russia in 2024. Another key operator, known as ‘Stallman,’ was the forum’s administrator at the time of the takedown.
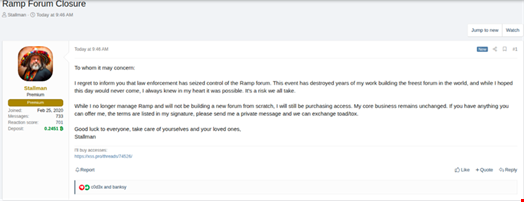
Rebecca Taylor, a threat intelligence researcher at Sophos, noted that Stallman "played a central role in maintaining trust, enforcing rules and managing the platform’s technical operations.” Stallman confirmed the takedown on the XSS forum, stating that it had “destroyed years of my work” and that there were no plans to rebuild.
Impact of the Takedown
The RAMP takedown is considered a significant disruption to criminal infrastructure. Giomar Salazaar, a threat intelligence analyst at Outpost24, called the takedown “another major blow to the infrastructure supporting the digital extortion ecosystem." Daniel Wilcock, a threat intelligence analyst at Talion, described it as "a big win for law enforcement," providing access to valuable information such as emails, IP addresses, and financial transactions.
However, Bohuslavskiy noted that the takedown will primarily impact low-tier actors and cause disruption to underground sellers, with minimal impact on top-tier groups. He also predicted that Telegram will absorb some of the displaced activity. Wilcock added that while RAMP's operator claims no plans to rebuild, other criminals are likely to turn to alternative underground markets.
The seizure of RAMP highlights the ongoing efforts of law enforcement to disrupt cybercriminal activities. However, the cybercrime ecosystem is resilient, and threat actors will likely adapt by migrating to other platforms or adopting new tactics.
As the cyber landscape evolves, Gopher Security remains dedicated to providing cutting-edge cybersecurity solutions. Our AI-powered, post-quantum Zero-Trust architecture converges networking and security across all environments, ensuring robust protection against emerging threats.
Explore our advanced cybersecurity solutions at https://gopher.security and contact us to learn how we can help safeguard your organization.





