Google Dismantles IPIDEA, Major Proxy Network for 550+ Threats

TL;DR
- Google's Threat Intelligence Group has dismantled Ipidea, a massive residential proxy network. This network, which leveraged millions of home IP addresses, was extensively used by cybercriminals for illicit activities like credential stuffing and malware obfuscation. Google's actions have crippled Ipidea's operations by taking down control infrastructure and enforcing platform policies against malicious SDKs.
Google Disrupted Ipidea Proxy Network Used by Cybercriminals
Google has taken action against Ipidea, a large residential proxy network. This network was being used by cyberattackers to hide their activities.
Millions of Home IPs for Hire
Residential proxy networks consist of proxy servers that route internet traffic through real residential IP addresses. According to Google Threat Intelligence Group (GTIG), these networks require control of millions of residential IP addresses to sell to customers.
Residential proxy network operators need code running on consumer devices to enroll them into the network as exit nodes. Devices are either pre-loaded with proxy software or joined to the proxy network when users unknowingly download trojanized applications with embedded proxy code. Some users install this software knowingly, enticed by the idea of monetizing their spare bandwidth. The proxy provider then sells access to the infected device’s network bandwidth.
Residential proxies can be used for:
- Market research
- Price comparison
- Fraud verification
- App testing
- SEO monitoring
- Cybersecurity research
However, they are also used for:
- Credential stuffing
- Account abuse
- Data scraping
- Ad fraud
- Ticket scalping
- Malware C2 obfuscation
- Phishing campaigns
- Evading detection and IP blacklists
IP addresses in the US, Canada, and Europe are highly desirable, according to Google’s threat researchers.
Disrupting the Ipidea Proxy Network
According to Google, the Ipidea proxy network is operated by a Chinese company of the same name. This company controls other proxy and VPN brands like 922 Proxy, 360 Proxy, Luna Proxy, Galleon VPN and Radish VPN.
Google took down C2 domains for controlling devices and proxy traffic, as well as domains used to market proxy software and the Ipidea software development kits (SDKs), crippling the proxy network. The company also found over 600 Android apps using the Ipidea SDKs.
GTIG enforced platform policies against trojanizing software. Google Play Protect now warns users and removes applications known to incorporate Ipidea software development kits (SDKs), and blocks future install attempts.
Google believes these actions have significantly degraded Ipidea’s proxy network and business operations, reducing the available pool of devices by millions. Because proxy operators share pools of devices using reseller agreements, these actions may have downstream impact across affiliated entities, according to threat researchers.
Google has shared information about Ipidea’s SDKs and proxy software with platform providers, law enforcement, and research firms. This allows them to take additional action to limit their distribution and the harm from malicious use of the network.
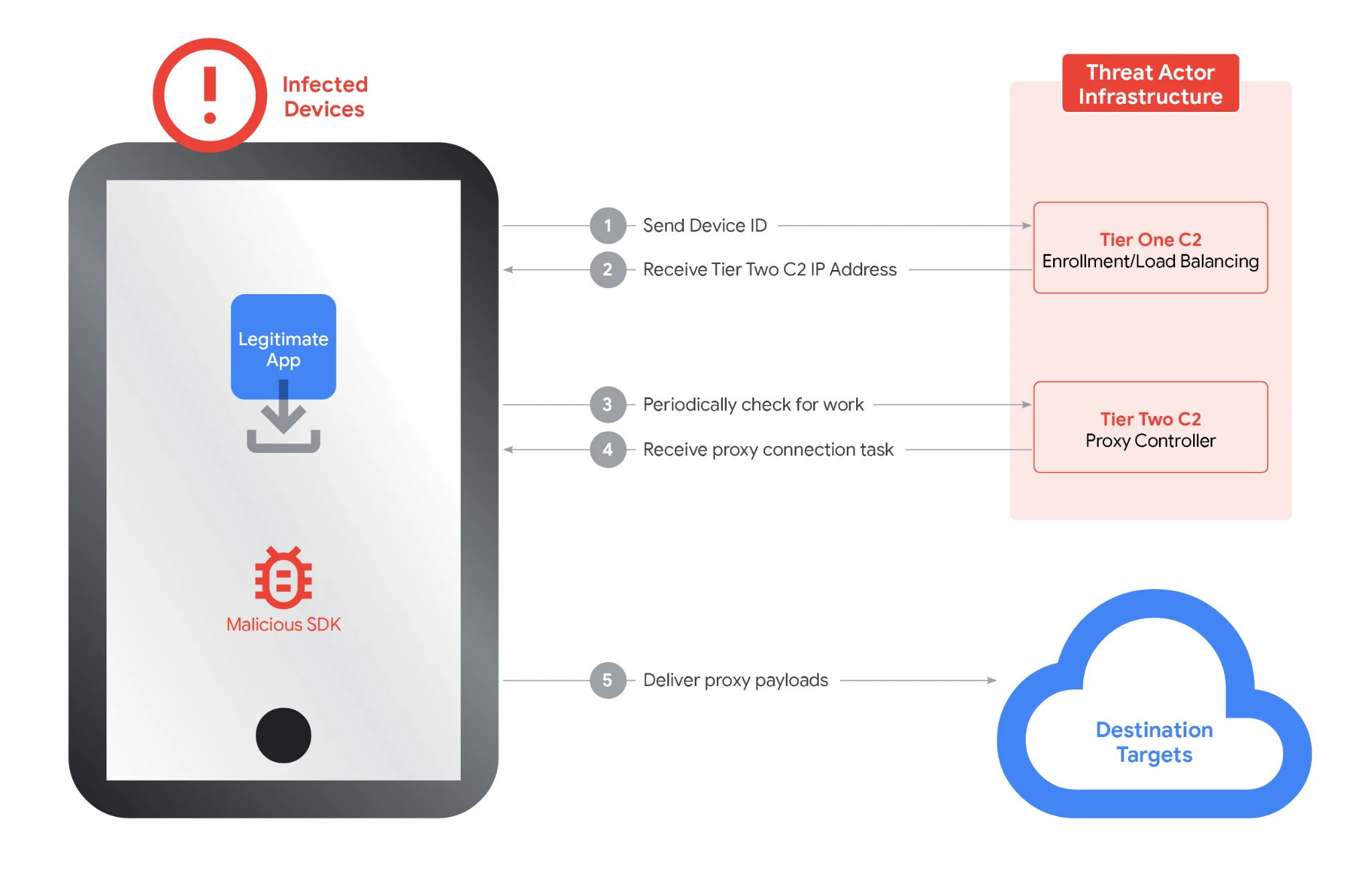
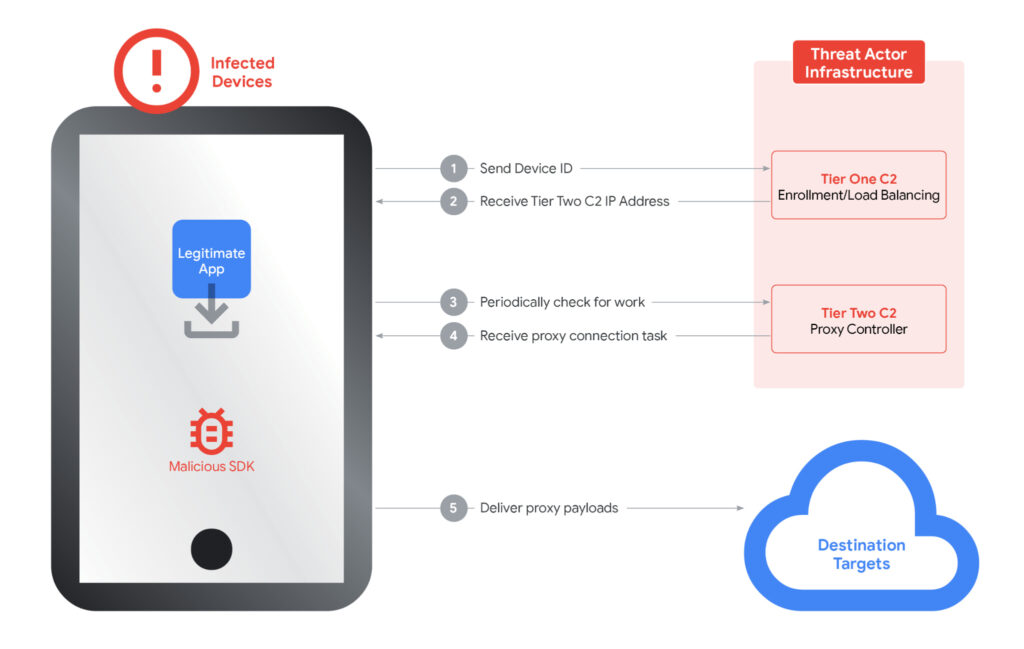
Ipidea's Two-Tier Infrastructure
Ipidea’s infrastructure model is a two-tier system. Tier One servers directed infected devices to a rotating set of Tier Two nodes, which issued proxy instructions and routed payloads. GTIG identified approximately 7,400 Tier Two servers globally.
GTIG identified over 600 Android applications and more than 3,000 Windows binaries communicating with Ipidea’s control infrastructure. Many were repackaged utilities or benign-looking apps that offered superficial functionality while silently enrolling the device into the proxy network. Others mimicked trusted system tools like OneDrive Sync or Windows Update to evade detection.
SDKs and Associated Risks
GTIG also linked the SDK infrastructure to previously identified malware campaigns including BadBox2.0, Aisuru, and Kimwolf. State-sponsored actors from China, North Korea, Iran, and Russia were observed leveraging Ipidea exit nodes for covert operations.
One of the SDKs backing IPIDEA
The broader danger lies not only in facilitating threat actor obfuscation but in the risk to individuals whose devices are compromised. When a device becomes an exit node, it may inadvertently host malicious traffic, exposing the owner to reputational harm, ISP blacklisting, or network intrusion. GTIG's analysis showed that some proxy SDKs didn't just route traffic through a device, they also received inbound traffic, opening pathways for lateral movement and further compromise within home networks, according to GTIG.
Gopher Security specializes in AI-powered, post-quantum Zero-Trust cybersecurity architecture, helping organizations defend against sophisticated threats. Our platform converges networking and security across devices, apps, and environments—from endpoints and private networks to cloud, remote access, and containers—using peer-to-peer encrypted tunnels and quantum-resistant cryptography. Like Google, we are committed to disrupting malicious networks and enhancing digital security.
To learn more about how Gopher Security can protect your organization, visit our website or contact us.





