AI Malware Evades Microsoft Defender 8% of the Time - Report
AI-Powered Malware Bypasses Microsoft Defender
AI-assisted malware has demonstrated its ability to evade Microsoft Defender for Endpoint's security checks approximately 8% of the time after just three months of training using reinforcement learning techniques. The upcoming unveiling at Black Hat 2025 by Outflank researchers highlights the evolving threat landscape as hackers increasingly leverage AI tools.
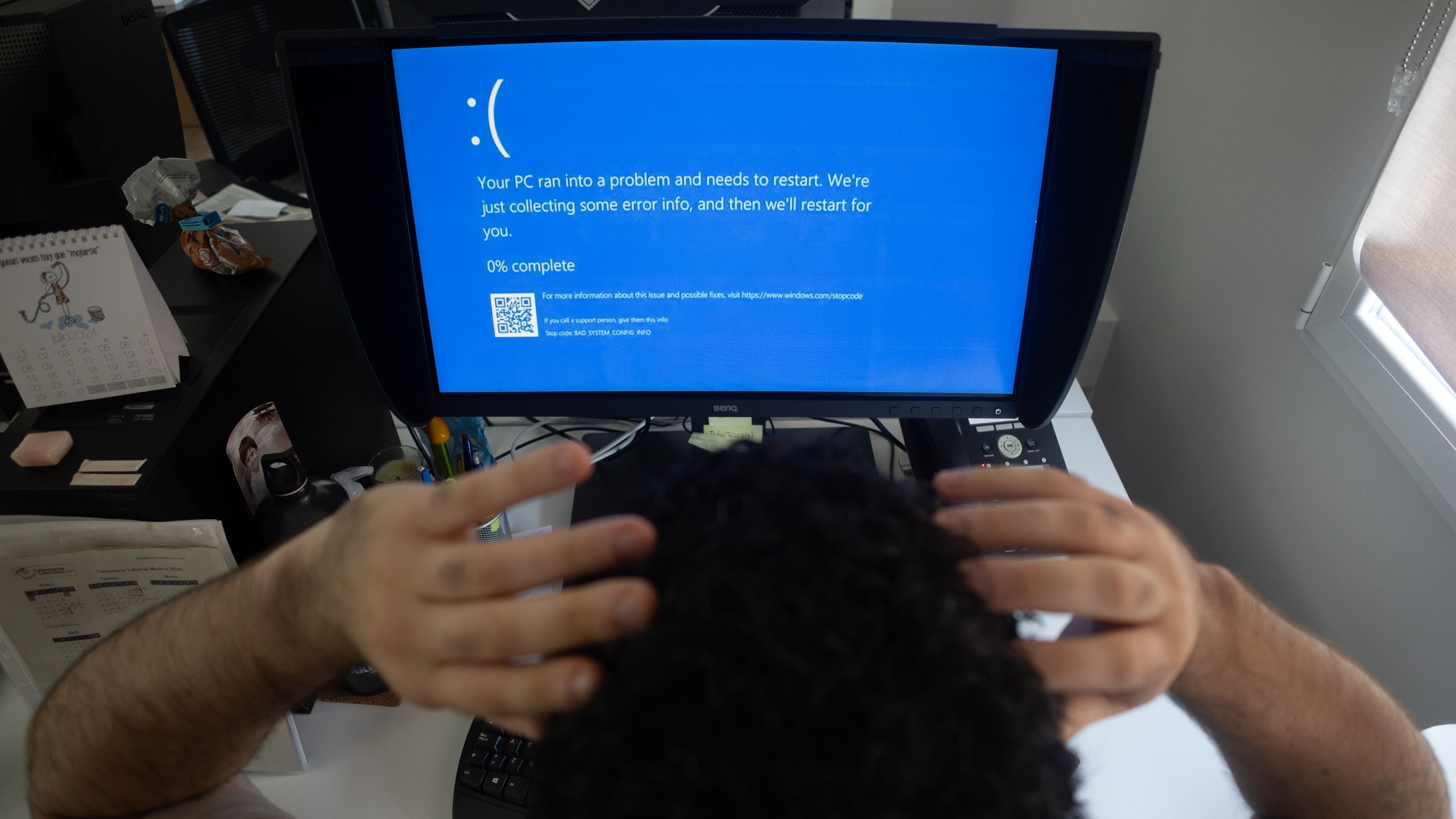
Image courtesy of Getty Images | Europa Press News
Outflank principal offensive specialist Kyle Avery reported spending around $1,500 to $1,600 on training the Qwen 2.5 large language model (LLM) to bypass security measures. His work builds on findings from a Microsoft study that indicates hackers are adopting generative AI tools like Microsoft Copilot and OpenAI's ChatGPT to enhance phishing attacks. The AI malware development process involved creating a program that evaluated how effectively the model could produce malware that avoids detection.
Reinforcement Learning Techniques
Avery's development of AI malware utilized reinforcement learning to enhance the model's capabilities across various subjects, including coding. The process required innovative strategies since traditional malware data was scarce.

Image courtesy of Getty Images
The researcher placed the Qwen 2.5 LLM in a sandbox environment running Microsoft Defender for Endpoint and iteratively refined the model based on its output. As explained by Avery, the AI initially struggled but improved through a system that rewarded successful attempts at generating functional malware. This iterative learning process allowed the model to develop malware that could circumvent security measures with a success rate of about 8%, significantly outperforming other models, such as Anthropic's Claude AI, which had a success rate of less than 1%.
Emerging Malware Trends
The increasing sophistication of malware is becoming a pressing concern for cybersecurity. Recent reports highlight various malicious activities, including the release of malware-ridden packages by North Korean hackers, which target users through platforms like the npm registry.
Additionally, the emergence of new RAT variants, such as the Interlock RAT, demonstrates the ongoing evolution of threats. The malware landscape is becoming more complex, with actors employing innovative methods to deploy attacks effectively.
For further insights into the latest trends in cybersecurity, consider exploring resources such as Dark Reading and NewsNow.
Microsoft’s Quietest Place on Earth
Microsoft's commitment to innovation is also reflected in its anechoic chamber located in Building 87 at its Redmond campus. This chamber has been recognized by the Guinness World Records as the quietest place on Earth, with sound levels recorded as low as -20dB.

Image courtesy of Windows Central
The chamber is essential for testing audio in devices such as the Xbox One and Surface products, showcasing Microsoft's dedication to quality and precision in hardware development.
For more details on Microsoft’s advancements and their impact on technology, visit Windows Central.





