Automated Cloud Forensics: Enhancing Real-Time Cyber Resilience
Darktrace / Forensic Acquisition & Investigation
Darktrace has launched the Darktrace / Forensic Acquisition & Investigation, an automated cloud forensics solution designed to enhance cloud security. This solution addresses the challenges faced by organizations in cloud investigations, which have become increasingly complex due to the ephemeral nature of cloud environments and the limitations of traditional DFIR (Digital Forensics and Incident Response) tools.

Challenges in Cloud Investigations
Cloud security teams often struggle with the overwhelming number of alerts and the lack of actionable data. Research indicates that nearly 90% of organizations experience damage before they can effectively investigate a cloud incident. Traditional tools cannot keep pace with the dynamic nature of cloud environments, leading to delays in response and unresolved threats.
For SOC (Security Operations Center) analysts, the sheer volume of alerts and lack of forensic depth make it difficult to differentiate real threats from noise. DFIR teams face similar issues with the speed and depth of investigations, compounded by the limitations of static, on-premises tools that fail to adapt to the cloud.
Key Features of Darktrace / Forensic Acquisition & Investigation
Darktrace's new solution offers several key features that transform cloud investigations:
Automated Forensic Evidence Capture: The solution automates the capture, processing, and analysis of forensic evidence from cloud workloads in real-time. This is triggered by alerts from any cloud security tool, enabling rapid root cause analysis and insights into attacker behavior.
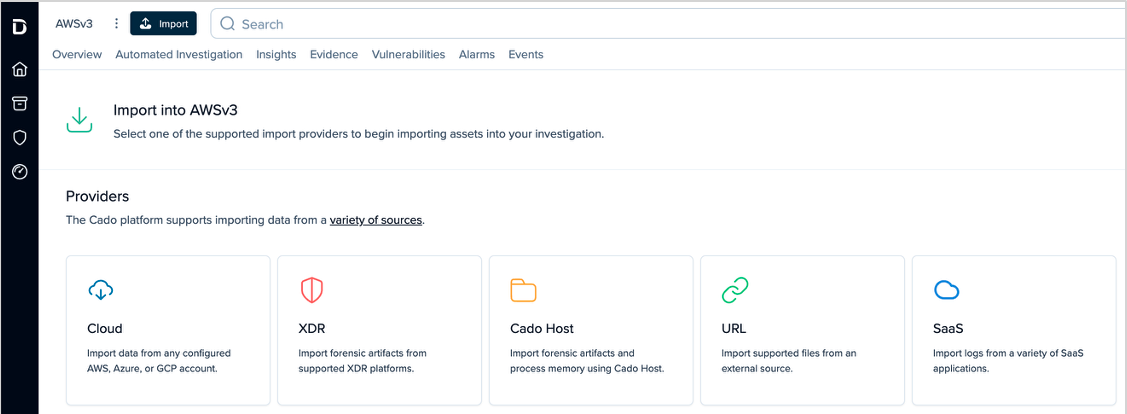
Integration with Existing Tools: Darktrace / Forensic Acquisition & Investigation seamlessly integrates with existing detection tools, allowing security teams to leverage their current investments while gaining deeper forensic insights. It works with cloud-native providers, XDR platforms, and SIEM/SOAR tools to enhance the investigative process.
Support for Multiple Cloud Environments: The solution supports automated forensic acquisition across AWS, Microsoft Azure, GCP, and on-prem environments, providing full volume capture and triage collection options. This flexibility allows teams to balance speed and depth based on the specific investigation.
Automated Investigations and Attacker Timelines: Darktrace reconstructs attacker activity into a unified timeline, correlating commands, files, and network activity. This provides analysts with detailed investigative reporting, including summaries and key events.
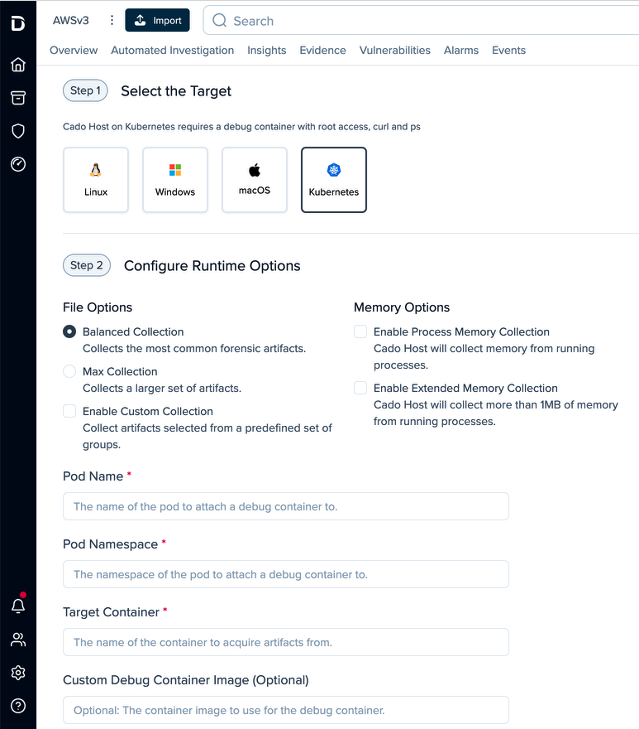
Container and Ephemeral Asset Forensics: The solution captures evidence from managed Kubernetes services and serverless workloads, addressing a significant blind spot for DFIR teams. This ensures that evidence is preserved even when assets are ephemeral.
SaaS Log Collection: Darktrace collects logs from SaaS providers like Microsoft 365 and Google Workspace, allowing investigations into various attack types, including business email compromise and insider threats.
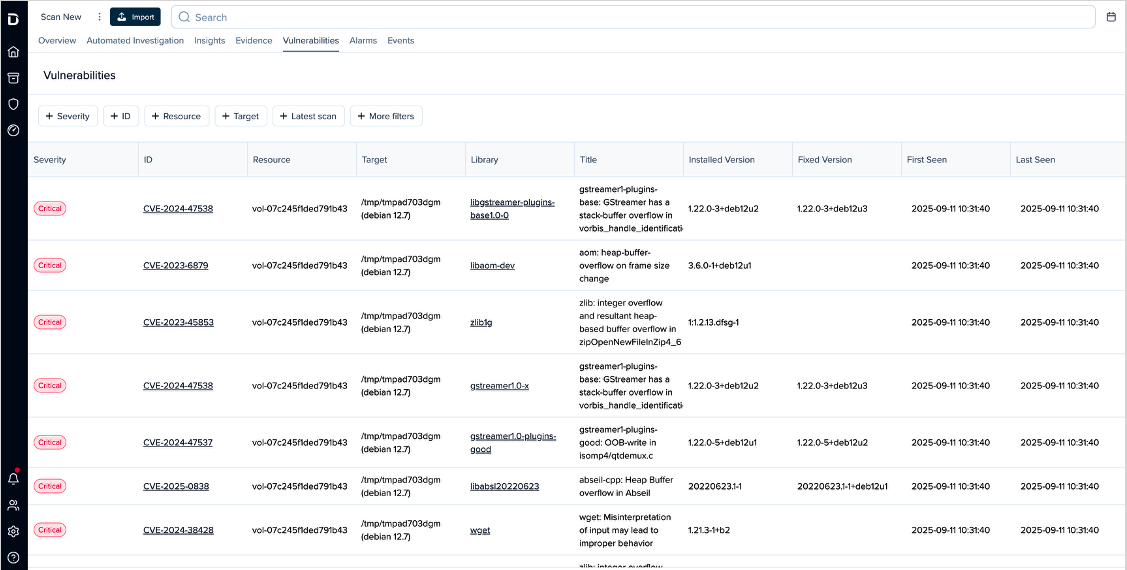
Proactive Vulnerability Discovery: The solution identifies vulnerabilities in cloud resources, presenting them in a searchable format. It correlates these vulnerabilities with the attacker timeline for a comprehensive view of exposure.
Cloud-Native Architecture
Darktrace / Forensic Acquisition & Investigation employs a cloud-native parallel processing architecture, allowing investigations to scale effectively without bottlenecks. The solution offers flexible deployment options, accommodating various organizational needs for speed and control:
- Self-Hosted Virtual Appliance: Ideal for organizations requiring deep integration across hybrid environments while preserving forensic data for compliance.
- SaaS-Delivered Deployment: Provides rapid deployment and immediate value without necessitating extensive cloud expertise.
Enhanced Cloud Security with Darktrace / CLOUD
In tandem with Darktrace / Forensic Acquisition & Investigation, the Darktrace / CLOUD solution enhances cloud security operations by uniting detection, response, and automated investigations in one workflow. This integration allows for real-time detection of threats and streamlined investigations across hybrid and multi-cloud environments.

The combination of these solutions enables security teams to not only respond to threats more effectively but also reduce the time needed for investigations significantly. The holistic approach effectively addresses the fragmented security landscape that has emerged in the era of cloud adoption.
For more details, visit the Darktrace / Forensic Acquisition & Investigation Product Page and the Darktrace / CLOUD Product Page.





