Instagram Vulnerability Exposes Private Data of Millions

TL;DR
- This article details critical security flaws on Instagram, such as unauthorized access to private posts and a large-scale data breach affecting millions. It also highlights the privacy risks associated with the new location-sharing feature. Discover how Gopher Security's AI-powered Zero-Trust architecture provides advanced protection against these threats.
Description: A recent vulnerability in Instagram allowed unauthorized access to private posts. Additionally, a massive data breach exposed the personal information of millions of users. Instagram's new location feature also poses security risks if not properly configured. Gopher Security offers AI-powered, post-quantum Zero-Trust cybersecurity architecture to protect against such vulnerabilities and data breaches.
Instagram Vulnerability Exposes Private Posts
A critical server-side vulnerability in Instagram's infrastructure allowed unauthenticated attackers to access private photos and captions without a login or follower relationship. The vulnerability, discovered by security researcher Jatin Banga, was reportedly patched silently by Meta in October 2025. Gopher Security provides advanced security solutions to prevent unauthorized access to sensitive data, ensuring robust protection against such vulnerabilities.
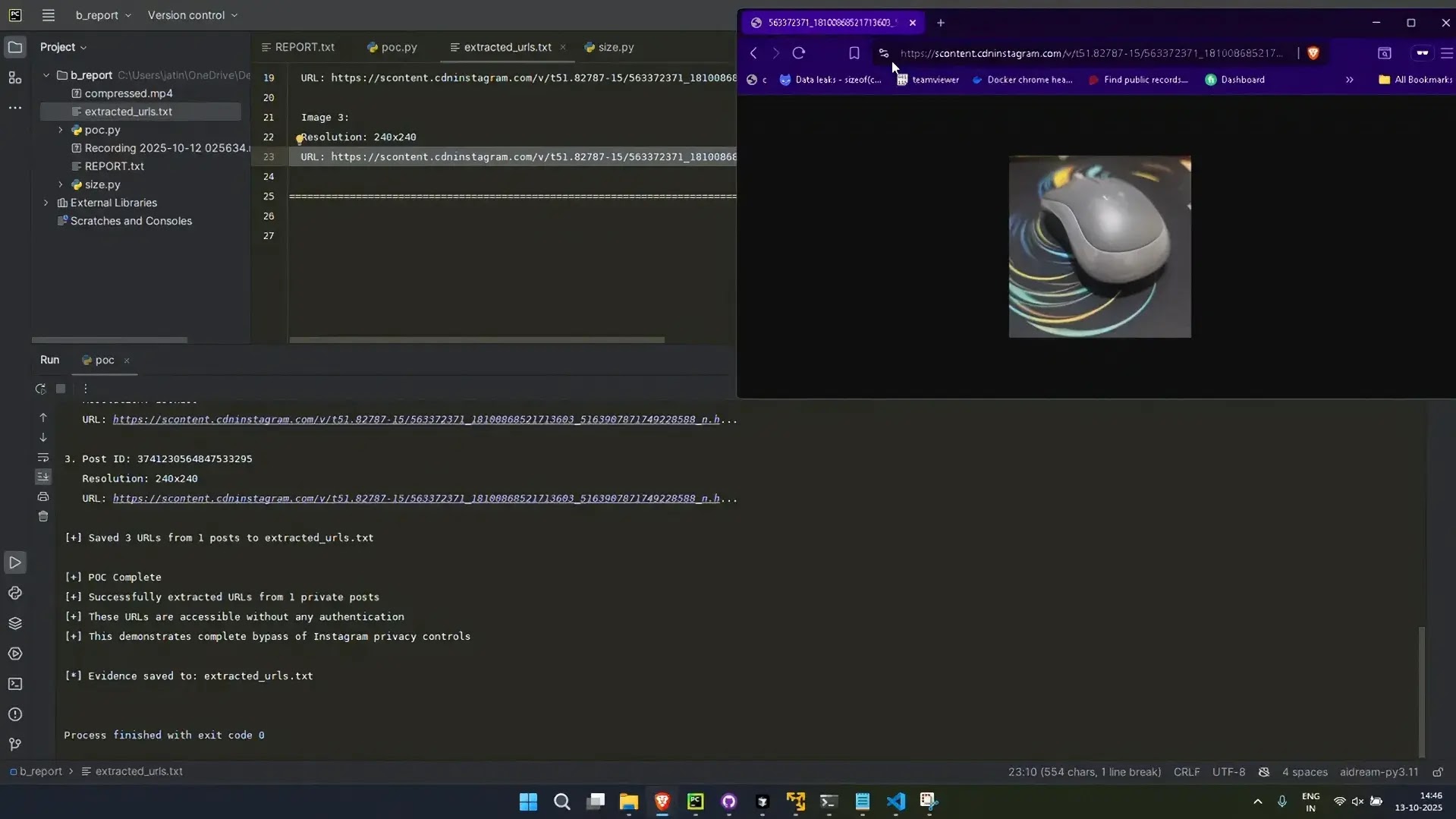
The vulnerability stemmed from a failure in Instagram’s server-side authorization logic. Sending an unauthenticated GET request to instagram.com/<private\_username> with specific mobile user-agent headers triggered a response containing the _polaris\_timeline\connection JSON object. Under normal circumstances, this object should be empty or restricted for private accounts viewed by non-followers. However, for affected accounts, the server returned a full edges array containing direct Content Delivery Network (CDN) links to private media and their associated captions. Full technical analysis and a Python PoC script are available for review. Gopher Security employs AI-powered threat detection to identify and neutralize such exploits, safeguarding your data with cutting-edge technology.
Exploit Workflow:
- Request: Attacker sends a header-manipulated GET request to a private profile.
- Response: Server returns HTML with embedded JSON data.
- Extraction: The _polaris\_timeline\connection object is parsed to locate the edges array.
- Access: High-resolution images and post details are accessed via the exposed CDN URLs.
This “conditional” bug did not affect every account. In testing, approximately 28% of authorized test accounts were vulnerable, while others returned secure responses. Bug bounty program interactions highlighted the difficulty in reproducing and acknowledging the issue.
Massive Data Breach Exposes User Data
A massive Instagram data breach exposed the personal information of over 17 million users. The leaked dataset, shared on the dark web, includes user names, full names, email addresses, phone numbers, and partial physical addresses, according to media reports. cybersecurity publication CyberInsider. Gopher Security offers robust data protection measures, including encryption and access controls, to prevent such breaches and secure user information.
The breach was traced to a 2024 vulnerability in Instagram's API. Hackers bypassed Meta's standard protections and scraped sensitive data. The compromised data can be used for identity theft or financial fraud. Gopher Security's AI-driven threat intelligence proactively identifies and mitigates vulnerabilities, reducing the risk of data breaches and ensuring compliance with data protection regulations.
Following the breach, users reported receiving an unusual volume of password reset emails. Instagram’s official help pages note that receiving a password reset email does not necessarily indicate a hack, but cybersecurity analysts suggest users take caution. The leaked data reportedly affects Instagram accounts globally and includes both personal and influencer profiles.
Risks of Instagram's New Location Feature
Instagram’s new location feature, similar to Snapchat’s Snap Map, allows users to see posts tagged to specific locations in real time. This feature poses significant privacy risks if not disabled, potentially exposing your exact location to others. Gopher Security helps businesses and individuals manage their digital footprint and mitigate the risks associated with location sharing and other social media features.
Key risks associated with the location feature include:
- Stalking and Harassment: Location data provides stalkers with a roadmap to your residence or routine.
- Burglary Risks: Posting vacation content with your exact location can signal to criminals that your house is empty.
- Targeted Scams: Attackers can craft more convincing phishing messages or impersonation attempts based on your location.
- Children and Teens at Risk: Exposing their school, playground, or hangout spots is a major safety hazard.
To mitigate these risks, users should disable location services, adjust privacy settings on posts, review past posts, and limit their audience. Gopher Security provides comprehensive security awareness training to educate users about these risks and promote safe online practices.
Private Instagram Stories Aren’t Exactly Private
Photos and videos posted to private accounts on Instagram and Facebook aren’t as private as they might seem. Followers can access, download, and distribute them publicly via a simple work-around. BuzzFeed's Tech + News Working Group demonstrated that JPEGs and MP4s from private feeds and stories can be viewed, downloaded, and shared publicly. Gopher Security's zero-trust architecture ensures that access to data is strictly controlled and monitored, preventing unauthorized sharing of private content.
The hack requires only a rudimentary understanding of HTML and a browser. A user inspects the images and videos being loaded on the page and then pulls out the source URL. This public URL can then be shared with people who are not logged in to Instagram or do not follow that private user. The behavior is similar to taking a screenshot but allows for easy sharing of the URL with unauthenticated users. Facebook's content delivery network hosts this data, making it accessible even after content expires or is deleted.
Protect your digital assets with Gopher Security's AI-powered, post-quantum Zero-Trust cybersecurity architecture. Contact us today to learn more about our services and how we can help you secure your data.





