Sygnia's CEO Replacement: A Second Change in Six Months
Sygnia Replaces CEO
Sygnia has replaced its CEO for the second time in six months. Guy Segal will take over the role soon after Avi Golan was appointed in March 2025. The reasons behind Golan's departure remain unclear.
Image courtesy of CTech by Calcalist
For more details, refer to Sygnia replaces CEO for the second time in six months and CTech news.
Guy Segal's Background
Guy Segal is the new CEO of Sygnia, overseeing the company's strategy and operations. With over 25 years in cybersecurity, Segal has significant experience in analytics and business leadership. He has previously held senior positions, including Head of APJ and initiator of Sygnia's Managed Detection and Response (MDR) practice.

Image courtesy of Sygnia
Prior to Sygnia, Segal was the General Manager at Custodio-Technologies and worked as Cyber Security Leader for IBM Security. He also served in Unit 8200, the IDF's elite cyber unit. Segal holds an EMBA from Ben-Gurion University and lectures on cybersecurity.
For more information on Segal, visit Guy Segal - Sygnia.
Sygnia's Leadership Team
Sygnia's leadership team has extensive expertise in cybersecurity and technology. Key members include:
- Adam Finkelstein, SVP of Global Client Leadership, oversees business development and security initiatives globally. More details can be found at Adam Finkelstein.

Image courtesy of Sygnia
- Adi Keinan, CFO, has over 20 years of experience in finance and corporate functions. More about him can be found at Adi Keinan.

Image courtesy of Sygnia
- Shoham Simon, SVP of Global Cyber Services, previously led incident response efforts. Additional information is available at Shoham Simon.

Image courtesy of Sygnia
For a complete overview of Sygnia's leadership, visit Sygnia's Leadership Team.
The Forensic Value of MFT Slack Space
MFT slack space in NTFS is crucial for digital forensics. It often goes unnoticed by standard forensic tools but can reveal vital file metadata, even in Windows 10 and 11 systems.

Image courtesy of Sygnia
The Master File Table (MFT) records essential file-system metadata. Each file has at least one MFT record, typically 1024 bytes, where slack space can remain unused. This unused space is called MFT slack space, which is often not visible to digital forensics software.
Deleted or securely wiped file metadata can be found in MFT slack space, making it critical for investigations. This is particularly significant for real-world incident response engagements, where recovery of metadata is often necessary.
Learn more about MFT analysis in The Forensic Value of MFT Slack Space.
Analysis Techniques
Parsing the MFT
Two notable open-source tools for parsing MFT are Eric Zimmerman's MFTECmd and Maxim Suhanov's dfir_ntfs. Both tools can recover file metadata from MFT slack space.
Tool Comparison: MFTECmd vs. dfir_ntfs
MFTECmd may detect possible slack index entries, whereas dfir_ntfs can recover more comprehensive information, including timestamps and file size. Suhanov's updates have improved detection mechanisms for partially overwritten entries.
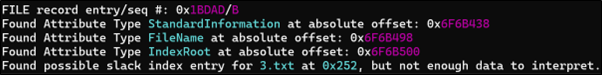
Image courtesy of Sygnia
Manual Analysis
Manual analysis using a hex editor can also be effective for specific directories. This has been beneficial for recovering critical information during incident response engagements.
Keyword Search
Searching for filenames as Wide Character strings in MFT files can help locate residual data, although this method may fail if the filename is partially or fully overwritten.
For further details on manual analysis and keyword searching, refer to The Forensic Value of MFT Slack Space.





