The Future of AI Cyber Security: Why Quantum-Resistant Encryption is Non-Negotiable

The "ten years away" myth for quantum computing died in March 2026. With recent, massive leaps in qubit coherence and error correction, the clock on our current cryptographic standards hasn't just started ticking—it’s screaming.
If your AI infrastructure still relies on RSA or ECC to protect your model weights and agentic communications, you aren't "behind the curve." You are currently operating in a state of terminal vulnerability. Quantum-resistant encryption (QRE) isn't some futuristic, "nice-to-have" item for a roadmap you’ll look at in 2030. It is the absolute floor for any organization that wants to keep its intellectual property private over the next eighteen months.
The 2026 Reality Check: Why the Timeline Collapsed
For years, the industry leaned on the comfortable lie of a decade-long buffer. We assumed scaling quantum hardware would remain a linear, agonizingly slow crawl. We were wrong. The "AI-Quantum" feedback loop has rewritten the math entirely. We aren't just waiting for hardware to catch up; we are using AI to optimize the very algorithms that threaten our security.
Modern AI research is now being applied to quantum error correction and gate synthesis, effectively compressing a decade of theoretical progress into a few quarters of engineering. When Shor’s Algorithm—the mathematical nightmare for current public-key infrastructure—hits a sufficiently powerful machine, it doesn’t just "crack" a key. It renders the entire concept of asymmetric encryption as we know it effectively transparent.
Why Traditional Encryption Fails Against Quantum AI
The physics gap here isn't just about raw computational power; it's about the nature of the math. RSA and ECC rely on the difficulty of integer factorization and discrete logarithms. These are puzzles that take classical computers an eternity to solve. But quantum computers? By leveraging superposition and entanglement, they can resolve them in minutes.
The acceleration factor is the most dangerous variable. By utilizing AI-powered quantum research, adversaries are bypassing the traditional, slow-moving testing phases of cryptographic attacks. They are training models to hunt for the most efficient paths to key derivation. Think about that: your "secure" channel is being mapped by an intelligence that never sleeps. If your security posture is static, you are essentially holding a paper shield against a directed energy weapon.
Why is "Harvest Now, Decrypt Later" (HNDL) an Immediate Business Threat?
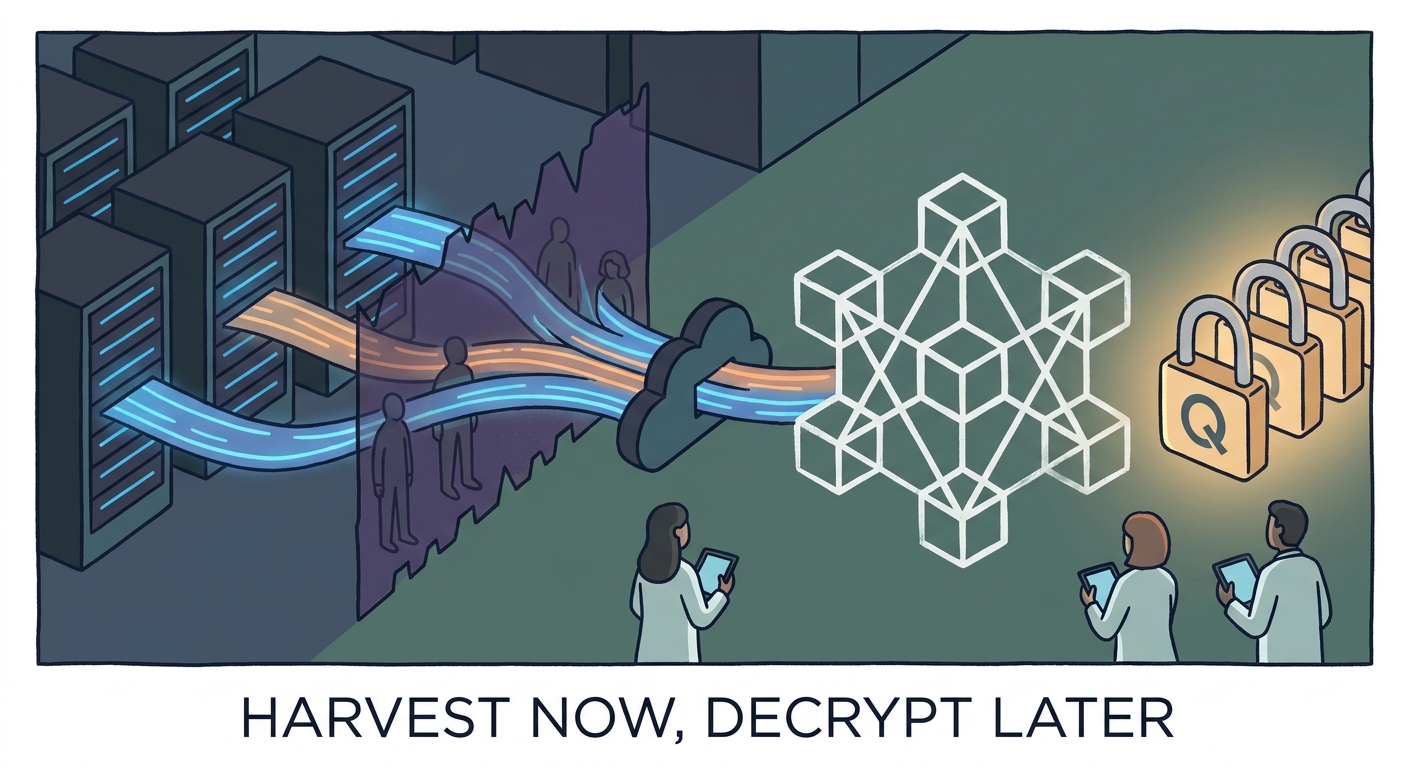
The most dangerous delusion among CISOs is the belief that a quantum threat requires a quantum computer to be active today. This ignores the grim reality of the "Harvest Now, Decrypt Later" (HNDL) strategy. As documented in detail by CISA’s guidelines on the HNDL threat, state actors and industrial competitors are vacuuming up massive troves of encrypted traffic, proprietary model weights, and sensitive training datasets right now.
They don't need to break your encryption today. They just need to store your data until they can. If your AI model’s intellectual property—that "secret sauce" of your training weights—has a business value that lasts longer than three to five years, it is already compromised. HNDL turns your long-term data security into a ticking time bomb. Every byte of proprietary model data sent over standard TLS is a future gift to your adversaries.
How Does the Model Context Protocol (MCP) Expand the Attack Surface?
As we pivot toward agentic architectures, the Model Context Protocol (MCP) has become the essential "connective tissue" for AI agents to talk to data sources and tools. But this convenience comes with a heavy security tax. MCP creates a web of inter-agent communication, often crossing internal and external boundaries, which effectively expands your attack surface exponentially.
In a post-quantum world, standard TLS protocols used to secure these MCP nodes are basically glass. If an adversary intercepts the context flow between your orchestration layer and your agents, they aren't just stealing a password. They are gaining the ability to manipulate the agent’s decision-making process or exfiltrate the entire context window. For those architecting these systems, understanding the nuances of Post-Quantum AI Infrastructure Security is the only way to ensure your agentic workflows aren't functioning as backdoors for future quantum actors.
Are You Prepared for the Shift to Crypto-Agility?
Crypto-agility is the ability to swap cryptographic primitives without tearing down your entire house. If your current AI pipeline is hard-coded to specific, aging encryption libraries, you are flirting with disaster. The shift isn't just about changing an algorithm; it's about building a modular architecture where NIST-approved algorithms like ML-KEM and ML-DSA can be swapped in as standard practice.
The NIST Post-Quantum Cryptography Standardization project provides the bedrock for this, but the implementation is on you. You need to move toward a "Modular Cryptography Layer" where your AI training pipelines and communication protocols are decoupled from the underlying encryption math. This allows you to update your security posture as new, more efficient, or more secure lattice-based algorithms emerge, without the need to re-architect your entire training environment from scratch.
What is the Step-by-Step Roadmap for CISOs?
Transitioning to a quantum-resistant posture is a multi-phase endeavor that requires immediate executive buy-in.
Phase 1: Audit the "Quantum Exposure" You cannot protect what you cannot see. Conduct a comprehensive audit of your AI model training data, model weights, and all endpoints using the Model Context Protocol. Determine which data has a shelf-life exceeding the three-year window; that data is your primary target for HNDL attacks.
Phase 2: Prioritize High-Value Agentic Infrastructure Not all nodes are created equal. Identify your MCP nodes that handle high-value proprietary logic or sensitive user data. If you are serious about hardening your stack, Building Quantum-Proof AI Infrastructure is the recommended path for prioritizing these critical nodes before moving to the wider edge.
Phase 3: Implementation of Crypto-Agile Perimeters Adopt a software-defined perimeter approach that allows for the rapid deployment of PQC-compliant tunnels. As outlined in Cloudflare's Post-Quantum Roadmap, the goal is to implement a hybrid security model—using both classical and post-quantum algorithms—to ensure that your systems remain secure even if one layer is found to have a vulnerability.
Conclusion: Compliance as a Competitive Advantage
Waiting for the "perfect" quantum-resistant standard is a fool’s errand. In the world of AI security, proactive adoption is a massive competitive advantage. It’s a signal to your partners, customers, and investors that you treat the longevity and integrity of your intellectual property with the seriousness it deserves.
The cost of inaction—the potential for mass exfiltration of your proprietary AI models—far outweighs the initial complexity of migrating to a crypto-agile stack. By treating security as a pillar of business continuity rather than a checkbox for compliance, you ensure that when the "quantum day" arrives, your organization remains standing while your competitors are scrambling to explain why their most valuable assets have been sitting in an adversary’s storage for years. For further strategic guidance, consult The CISO’s Guide to Post-Quantum AI Infrastructure Security to refine your long-term defensive posture.
Frequently Asked Questions
Does my AI model really need quantum-resistant encryption if it’s currently air-gapped?
Yes. Air-gapping is a hurdle, not a wall. History shows that internal threats, supply chain compromises, or even simple human error—such as data being moved for analysis on a non-gapped system—frequently breach air-gapped environments. If your model data is valuable enough to be air-gapped, it is valuable enough for an adversary to wait for an eventual transit vulnerability.
What is "Crypto-Agility" and why should a non-technical C-suite executive care about it in 2026?
Crypto-agility is the ability to change encryption methods quickly without needing to rebuild your entire software infrastructure. For the C-suite, this is a business continuity issue. Without it, you are locked into legacy protocols that will become obsolete, forcing a catastrophic and expensive "rip-and-replace" cycle when the quantum threat matures.
How does the Model Context Protocol (MCP) change the security requirements for AI agents?
MCP acts as a universal connector for agents, which means it inherently creates a wider, more complex attack surface. Because MCP allows agents to pull data from diverse sources, it requires a unified, post-quantum secure transport layer that traditional, siloed encryption cannot provide.
Is it possible to implement quantum-resistant encryption without replacing our entire legacy infrastructure?
Yes, by adopting a hybrid approach. You can wrap your legacy traffic in a quantum-resistant tunnel, effectively layering modern PQC over existing infrastructure. This "bridge" strategy allows you to gain the benefits of PQC immediately while you phase out legacy systems over time.