
Read the Gopher Security's Quantum Safety Blog
Cutting-edge insights on post-quantum cryptography, AI cybersecurity, and zero-trust architectures. The Gopher Security Blog explores advanced security solutions for Model Context Protocol (MCP), homomorphic encryption, and privacy-preserving technologies to future-proof your enterprise against emerging quantum and AI threats.
Featured


Model Context Protocol Security: Why Quantum-Resistant Encryption is Essential
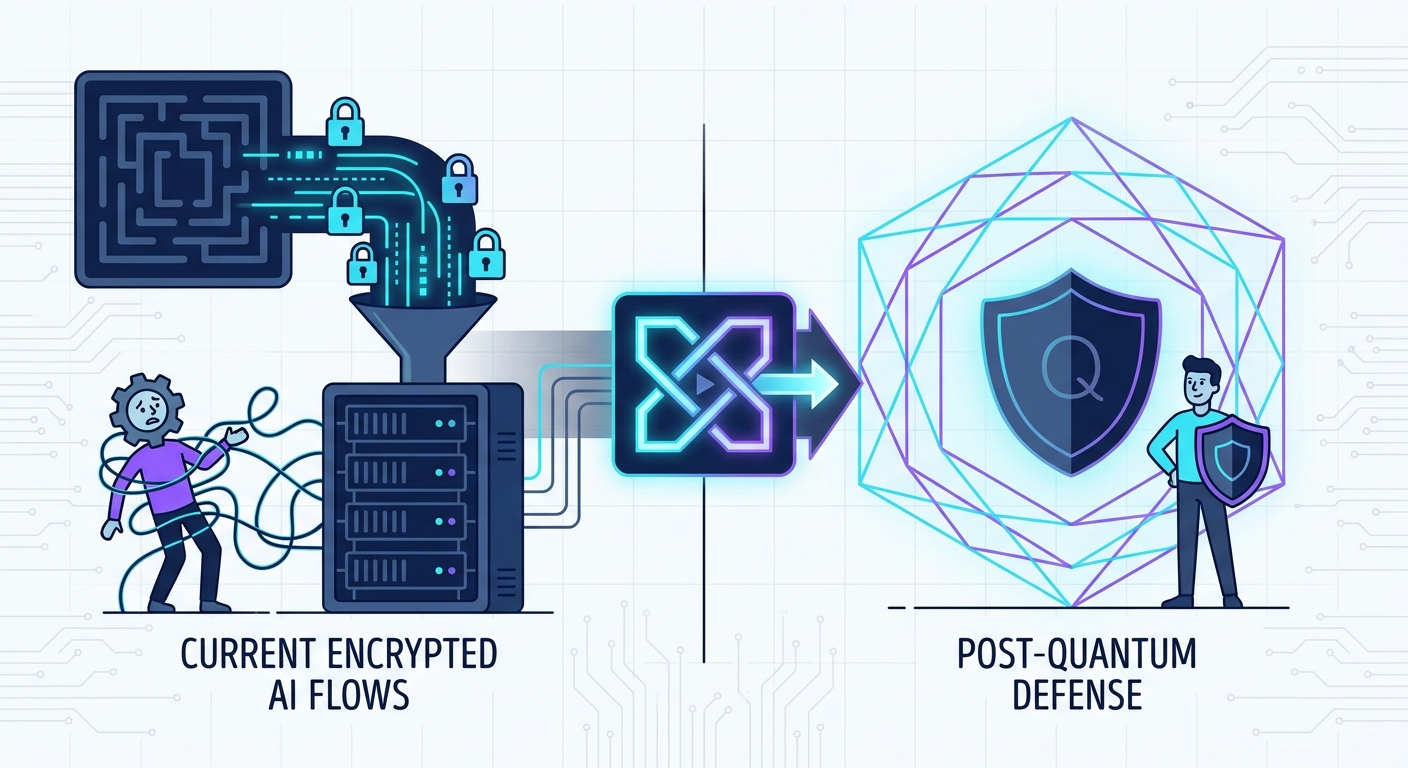
Future-Proofing AI: Integrating Post-Quantum Defense into Your Security Stack

Quantum Cyber: The Next Frontier in Enterprise AI Infrastructure Security
Articles
Post-Quantum AI Infrastructure Security: The Definitive Framework for 2026
Secure your AI infrastructure against quantum threats and MCP vulnerabilities. Discover our 2026 framework for quantum-resistant data protection and threat mitigation.

The 2026 Guide to Post-Quantum AI Infrastructure Security: Protecting MCP Deployments
Protect your AI infrastructure from the 'Store Now, Decrypt Later' threat. Learn how to secure your Model Context Protocol (MCP) deployments against quantum risks.
Quantum-Resistant Cryptography: A Blueprint for Securing AI-Driven Environments
Protect AI models from 'Harvest Now, Decrypt Later' quantum threats. Learn to implement hybrid, quantum-resistant cryptography for your AI infrastructure today.
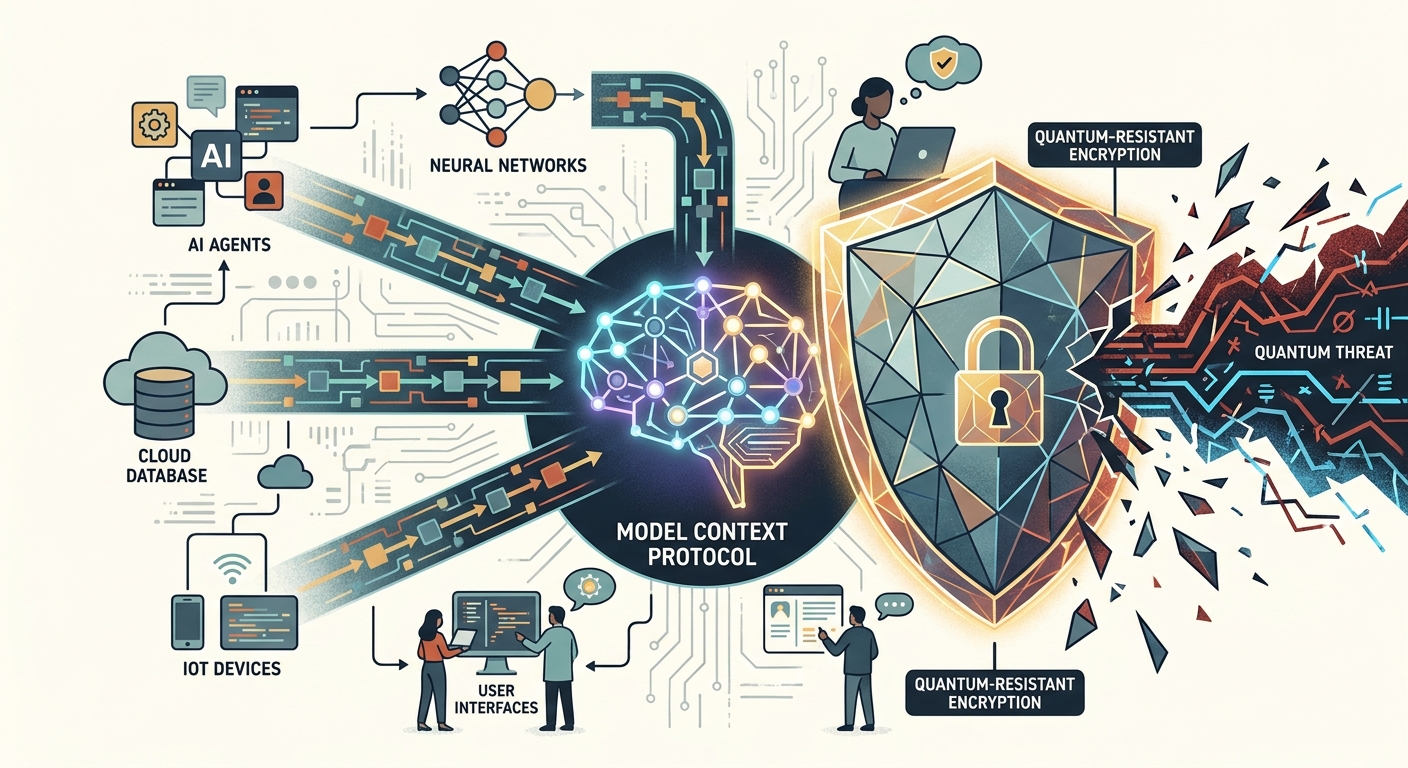
Implementing Quantum-Resistant Encryption in Model Context Protocol (MCP) Systems
Is your AI infrastructure quantum-ready? Learn how to implement quantum-resistant encryption in Model Context Protocol (MCP) systems to stop HNDL attacks.

5 Essential Pillars of Post-Quantum Security for Modern AI Infrastructure
Stop 'Harvest Now, Decrypt Later' attacks. Learn how to secure your AI infrastructure and Model Context Protocol (MCP) with NIST-standardized quantum cryptography.

How to Secure Model Context Protocol Deployments Against Quantum Attacks
Learn how to secure Model Context Protocol (MCP) deployments against Harvest Now, Decrypt Later quantum attacks to protect your sensitive enterprise AI data.
