Post-Quantum AI Infrastructure Security: A Complete Guide for 2026
Post-Quantum AI Infrastructure Security: A Complete Guide for 2026
Cutting-edge insights on post-quantum cryptography, AI cybersecurity, and zero-trust architectures. The Gopher Security Blog explores advanced security solutions for Model Context Protocol (MCP), homomorphic encryption, and privacy-preserving technologies to future-proof your enterprise against emerging quantum and AI threats.
Post-Quantum AI Infrastructure Security: A Complete Guide for 2026
Is Your AI Infrastructure Ready for 2026? A Guide to Post-Quantum Resilience

Protecting AI-Driven Environments: 5 Strategies for Post-Quantum Security

How to Secure Model Context Protocol Deployments Against Quantum Threats
Top 7 Quantum-Resistant Encryption Methods for Modern AI Pipelines

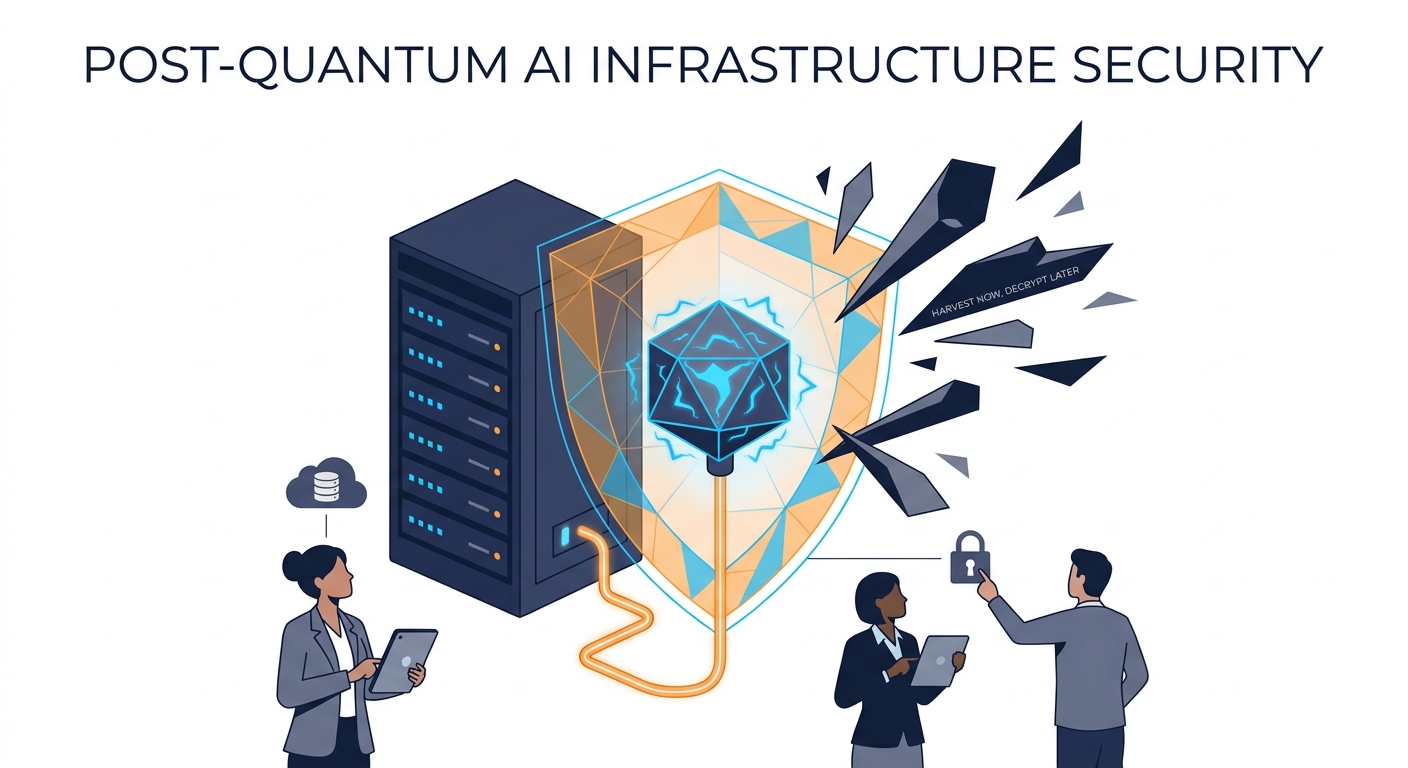
Beyond Traditional Defense: Why AI Systems Need Quantum-Proof Cryptography Now

The 2026 Roadmap to Post-Quantum AI Infrastructure Security
How to Secure MCP Deployments Using Quantum-Resistant Cryptographic Algorithms
What is Post-Quantum AI Infrastructure Security and Why Does Your MCP Need It?